Information And Data Security: Why ISO/IEC 27001:2022 Should Be A Strategic Priority For Businesses From The Beginning Of The Year
According to Viettel Cyber Security, in the third quarter of 2025 alone, Vietnam recorded more than 6.5 million compromised personal accounts, nearly 4,000 fraudulent domains, and over 547,000 DDoS attacks. Moreover, the level of sophistication continues to increase due to the application of AI-based techniques.
These figures do not merely reflect technological risks. Instead, they point to a clearer reality: information security has become a business risk. It now directly affects operations, corporate reputation, and long-term growth potential.
For SMEs in particular—organizations that are accelerating digital transformation but have not yet standardized their governance systems—the risks do not come only from external attacks. In many cases, vulnerabilities arise from the way data is created, used, and controlled on a daily basis.
As the new year begins, the key question is no longer whether a business will be attacked. Rather, it is where the organization stands on the information security risk landscape—and who will be accountable when an incident occurs.
ISO/IEC 27001:2022 – From Technical Protection To Data Risk Governance
Many organizations still approach ISO/IEC 27001 as a technical exercise. They focus on adding security tools, strengthening systems, or meeting audit requirements imposed by partners. As a result, the role of the standard is narrowed, and its real value is not fully realized.
In fact, ISO/IEC 27001:2022 is an information security management framework at the organizational level. It treats data as a strategic asset that requires governance comparable to finance, human resources, or the supply chain.
Through the implementation of an Information Security Management System (ISMS), organizations are able to:
• Identify information assets that are directly linked to revenue, reputation, and business continuity
• Assess risks based on actual impact, rather than reacting after incidents occur
• Clearly define security roles and responsibilities across management levels and departments
From this perspective, data protection is no longer the sole responsibility of the IT department. Instead, it becomes an integral component of overall corporate governance. This approach enables leadership to identify risks early and make proactive decisions.

ISO/IEC 27001:2022 – From technical protection to data risk governance
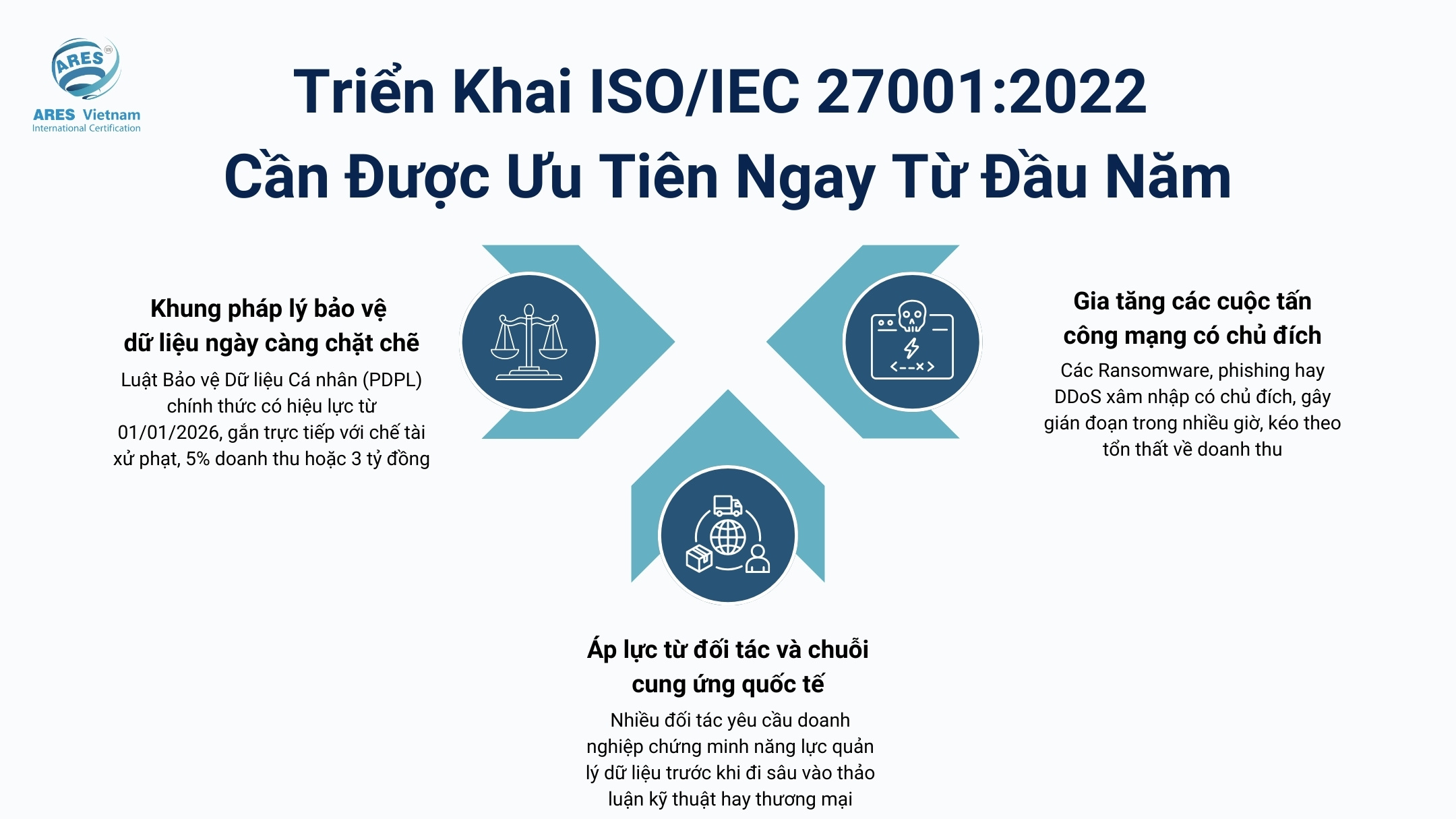
Why ISO/IEC 27001:2022 Should Be Prioritized From The Start Of the Year
At the beginning of a new operating cycle, information security is no longer an isolated operational issue. Instead, it directly influences management decisions, especially as businesses face pressure from multiple directions.
1. Increasingly stringent data protection regulations
Vietnam’s Personal Data Protection Law (PDPL), which takes effect on January 1, 2026, fundamentally changes the approach to data protection responsibility. Compliance is no longer limited to internal rules. It is now directly linked to regulatory sanctions, which may reach up to 5% of revenue or VND 3 billion.
Meanwhile, many organizations still manage data in a fragmented manner. Coordination between departments remains limited, and unified control mechanisms are often absent. Consequently, the gap between legal requirements and implementation capability has become a tangible risk.
2. Growth of targeted cyberattacks
Ransomware, phishing, and DDoS attacks are no longer rare scenarios. A single incident can disrupt systems for hours, resulting in losses in revenue, reputation, and customer trust.
In this context, addressing incidents individually is no longer effective. Without a consistent management framework, organizations struggle to accurately assess risk levels and prioritize appropriate control measures.
3. Pressure from international partners and supply chains
Within cross-border supply chains, information security is increasingly used as a screening criterion at the early engagement stage. Many partners require organizations to demonstrate data governance capability before entering technical or commercial discussions.
In many cases, companies only recognize this requirement after cooperation opportunities have already emerged. At that point, preparation time for audits is limited. As a result, project timelines are delayed, or businesses are excluded early, despite competitive capabilities and pricing.
Given these converging pressures, ISO/IEC 27001:2022 should be incorporated into implementation plans from the beginning of the year. The objective is not merely compliance, but the establishment of a stable data governance foundation for long-term growth.
The Implementation of ISO/IEC 27001:2022 Should Be Prioritized from the Beginning of the Year
A Structured Approach To Implementing ISO/IEC 27001:2022 Across Governance Areas
Effective implementation of ISO/IEC 27001:2022 does not lie in completing a checklist. Instead, it depends on building a system that can be measured, operated, and continuously improved.
1. Data – Correctly identifying assets that require protection
Many organizations have not clearly identified their core data, such as customer information, financial records, or intellectual property. When data leakage occurs, the consequences extend beyond technical issues to legal and reputational risks.
Recommended approach:
• Establish an inventory of data groups that directly support business activities
• Classify data according to sensitivity levels
• Define access rights based on job roles

2. IT infrastructure – Ensuring resilience and recovery capability
In many SMEs, IT infrastructure has evolved based on immediate needs. Operational indicators and documentation are often insufficient. As a result, assessing readiness during incidents becomes difficult.
Recommended approach:
• Review all systems, including servers, devices, and platforms
• Establish backup mechanisms integrated with access control
• Define and test recovery time objectives

3. People – Controlling risks arising from daily work habits
Most incidents originate from human factors, such as sending data to the wrong recipients, uncontrolled storage, or non-compliant remote work practices.
Recommended approach:
• Provide information security awareness training for all employees
• Assign security responsibilities based on specific roles
• Conduct simulation exercises to evaluate real-world responses

4. Partners and supply chains – Expanding the scope of governance
Partners and suppliers often have access to data but are not subject to the same level of control as internal staff.
Recommended approach:
• Identify partners involved in data processing or system access
• Clearly define security obligations in contracts
• Update assessments whenever access scope changes

5. Continuous improvement – Sustaining value beyond certification
ISO/IEC 27001:2022 is not a short-term project. Only through regular reviews and continual improvement can the system keep pace with changes in technology and operations.
Practical Value Of Early ISO/IEC 27001:2022 Implementation
The value of ISO/IEC 27001:2022 is not reflected solely in the certificate. Instead, it becomes evident during system operation.
• Reduced incidents and downtime: Organizations move from reactive responses to structured detection and handling, limiting the impact scope when incidents occur.
• Controlled risk-related costs: Early risk identification allows for appropriate allocation of preventive resources and reduces unexpected remediation costs.
• Standardized IT operations: Backup, access control, and system monitoring are managed consistently, reducing dependence on individuals or isolated departments.
• Proactive PDPL compliance: Clear data management processes provide evidence of compliance during inspections or dispute resolution.
Early implementation enables leadership to observe these improvements from the beginning of the year. At the same time, it clarifies return on investment and system readiness against potential risks.
Starting The New Year with A Proactive Security Mindset
Information security is not about incident response alone. It is a matter of governance priority. The longer organizations delay standardizing data management, the higher and less controllable the cost becomes when risks materialize.
Therefore, ISO/IEC 27001:2022 should not be viewed as a later-stage project. Initiating implementation from the start of the year allows organizations to proactively manage risks, meet legal requirements, and respond confidently to increasingly stringent expectations from markets and partners.
What should organizations do next?
Before discussing certification, organizations should clearly assess their current data management and information security practices. ARES Vietnam recommends starting with a practical assessment to identify risks, evaluate readiness levels, and develop a suitable ISO/IEC 27001:2022 implementation roadmap.
Contact ARES Vietnam for a readiness assessment and tailored consulting on ISO/IEC 27001:2022 implementation.
Related news

Important Update for Food Businesses: From 2026, HACCP, ISO 22000, and FSSC 22000 Will Not Replace the Food Safety Eligibility Certificate
Read more


Looking Back at the Journey of 2025 – A Year of Value and Trust
Read more


International ISO Certification Standards
Read more


ARES Vietnam Awards ISO 9001:2015 Certification To Dong Nguyen Design Construction Co., Ltd.
Read more


Lunar New Year of Binh Ngo 2026 – Sustaining Values, Shaping Standards
Read more













